CYBV481
Social Engineering Attacks & Defenses
Course Description
CYBV 481 will provide students with an advanced analysis of the tactics, techniques, and tools used to conduct and defend against Social Engineering attacks. A survey of why social engineering attacks are among the most effective Cyber-attack mechanisms and what can be done to mitigate them will be presented. Students will use interactive exercises to master social engineering attacks and defenses in order to be able to develop policies and procedures to increase organizational security posture.
Learning Outcomes
The student will:
- Identify and describe how the principles of Influence and Manipulation can be used to trick a user into violating a security policy.
- Evaluate and apply the different types of delivery methods that can be used in a social engineering campaign.
- Analyze how seemingly legitimate files can be used to compromise a user’s computer.
- Demonstrate how the browser is the most dangerous avenue for malware infection.
- Successfully apply the mitigation strategies that are used to defend the human from a social engineering attack.
- Successfully apply the mitigation strategies that are used to defend the endpoint and network from a social engineering attack.
- Identify and explain how Ethical Hacking and Social Engineering tests can be used to improve an organization’s overall security posture.


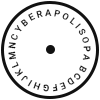 Cyberapolis
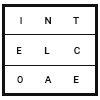
Cyberapolis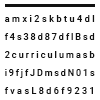 Curriculum
Curriculum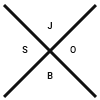 Career
Career Faculty
Faculty