CYBV436
Counter Cyber Threat Intelligence
Course Description
CYBV 436 will provide students with an in-depth examination of the tactics, techniques and procedures used to conduct online anonymization and attribution. An extensive analysis of the concepts, technologies, and best practices will be presented. Students will use interactive activities to become familiar with and practice the protection of their online identity.
Learning Outcomes
The student will:
- Analyze the challenges with online anonymity and attribution.
- Evaluate and apply the tactics, techniques, procedures and tools used to manage network signatures.
- Create and manage online virtual personas.
- Demonstrate the detection, classification, and identification of online threat virtual and physical personas.
- Apply the techniques and tools required to analyze images, files, and metadata.
- Successfully manage and conduct online attribution operations.
- Evaluate and apply the legal, policy and ethical issues surrounding virtual personas.


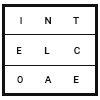
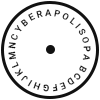 Cyberapolis
Cyberapolis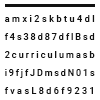 Curriculum
Curriculum Career
Career Faculty
Faculty